
Security is always at the top of a CIO's priority list and with the advent of BYOD and massive data breaches in the news, it's more worrisome than ever. Lisa Phifer at TechTarget published "Five Ways to Boost Mobile Application Security" to help IT departments think through some of the most pressing security concerns around mobile apps and device security.
Phifer warns readers: "When it comes to mobile application security, IT should focus on data, not devices." She encourages IT departments to ensure mobile app security by moving policies beyond mobile device management to these five areas:
1) Leverage Mobile Application Management (MAM) - MAM can stop users from sideloading public apps from unofficial app stores and it can silently push enterprise apps onto enrolled devices.
2) Apply containerization - Technologies that create authenticated, encrypted trustworthy environments to store, use and share business data can greatly boost security.
3) Insulate devices with Mobile Content Management (MCM) - MCM provides an authenticated encrypted lockbox where users can store business documents, images, email attachments, messages and more.
4) Practice reputation analysis - Reputation analysis, often included in Enterprise Mobility Management suites, can help assess and respond to mobile app vulnerabilities and threats faster.
5) Adopt identity management - Identity management allows IT to apply mobile application security policies based on authenticated user identity, and can potentially improve the user experience with single sign-on, for frictionless mobile access.
Read the full TechTarget article.
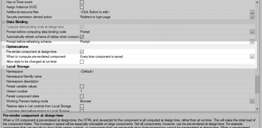
Read how the Alpha Anywhere Security Framework secures web and mobile apps for developers.






Comment