Marty Resnick and Adrien Leow of Gartner Research just released a report on mobile app development with some great points. "Treat Mobile Apps as Products, Rather Than Projects, to Maximize Their Value" advises application developers to apply product management principles to optimize applications' ROI, increase their adoption and reduce end-user abandonment. They declare:
The report goes on to explain that if you don't break from business as use the app risks becoming detached from the user experience, hurting application adoption and retention by users. The caution readers that the application needs to be "economical, targeted and business-function-specific." They also remind users to remove functions that users aren't accessing and add the functions they're more likely to use. To achieve this, Gartner stresses an iterative process used in product management:
"Business as usual risks negatively affecting application adoption and user retention."
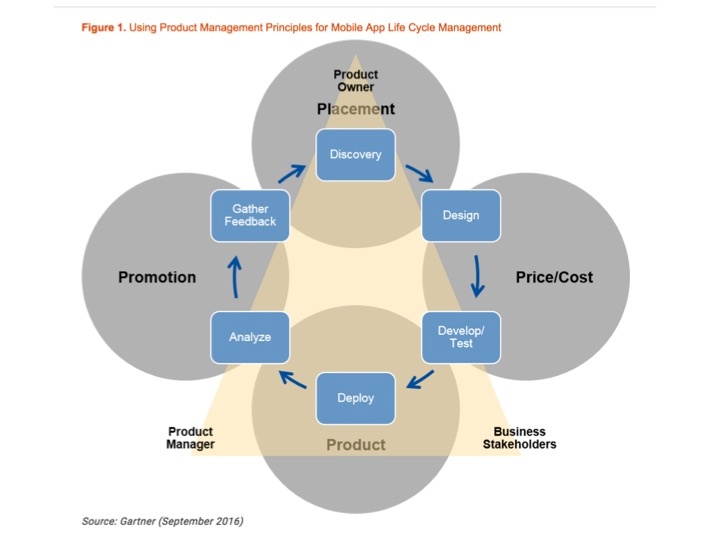
The report goes on to explain that if you don't break from business as use the app risks becoming detached from the user experience, hurting application adoption and retention by users. The caution readers that the application needs to be "economical, targeted and business-function-specific." They also remind users to remove functions that users aren't accessing and add the functions they're more likely to use. To achieve this, Gartner stresses an iterative process used in product management:
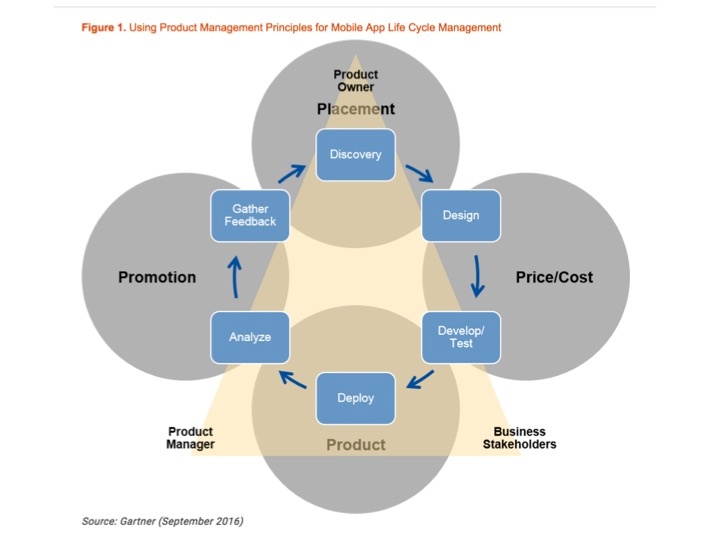
Gartner iterative product management process for app development. Source: "Treat Mobile Apps as Products, Rather Than Projects, to Maximize Their Value" September 2016
The team at Alpha Software believes that mobile and web apps should be easy to build and fast to update, so encourage an ongoing iterative process. We believe apps should be built quickly, easy for end-users to use, and should streamline and simplify everyday business processes. Our recent Alpha DevCon conference was testament to this focus.
Use the best app maker for building mobile apps.






Comment